IToddler: Difference between revisions
No edit summary |
Tag: Made through Tor |
||
| Line 13: | Line 13: | ||
== Origins == | == Origins == | ||
[[Brimstone|Apple products]] are generally known to be overpriced<ref>https://www.youtube.com/watch?v=VMOBTyJbu1A</ref><ref>https://www.youtube.com/watch?v=eKm5-jUTRMM</ref>, fragile<ref>https://www.youtube.com/watch?v=AUaJ8pDlxi8</ref><ref>https://www.youtube.com/watch?v=GuWUUTNg9r4</ref><ref>https://www.youtube.com/watch?v=44DEgUXREUQ</ref><ref>https://www.youtube.com/watch?v=0qbrLiGY4Cg</ref><ref>https://www.youtube.com/watch?v=AH5F73qPtQQ</ref>, unrepairable<ref>https://www.youtube.com/watch?v=7cNg_ifibCQ</ref><ref>https://www.youtube.com/watch?v=qV4_mLw2BGM</ref><ref>https://www.youtube.com/watch?v=iiCBYAP_Sgg</ref><ref>https://www.youtube.com/watch?v=MUifN6abtSI</ref><ref>https://www.youtube.com/watch?v=RIFQC8iA65k</ref><ref>https://www.youtube.com/watch?v=RYG4VMqatEY</ref>, lacking in security<ref>https://www.kaspersky.com/blog/iphone-illusion-of-security/49145/</ref><ref>https://google.github.io/security-research/pocs/linux/bleedingtooth/writeup.html</ref><ref>https://www.youtube.com/watch?v=whhPipa6sBc</ref><ref>https://www.youtube.com/watch?v=FCSCq5rGxDI</ref><ref>https://googleprojectzero.blogspot.com/2023/10/an-analysis-of-an-in-the-wild-ios-safari-sandbox-escape.html</ref><ref>https://googleprojectzero.blogspot.com/2022/04/cve-2021-1782-ios-in-wild-vulnerability.html</ref><ref>https://googleprojectzero.blogspot.com/2021/12/a-deep-dive-into-nso-zero-click.html</ref><ref>https://googleprojectzero.blogspot.com/2020/12/an-ios-zero-click-radio-proximity.html</ref><ref>https://googleprojectzero.blogspot.com/2020/01/remote-iphone-exploitation-part-1.html</ref><ref>https://googleprojectzero.blogspot.com/2020/01/remote-iphone-exploitation-part-2.html</ref><ref>https://googleprojectzero.blogspot.com/2020/01/remote-iphone-exploitation-part-3.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/implant-teardown.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-1.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-2.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-3.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-4.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-5.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/a-very-deep-dive-into-ios-exploit.html</ref><ref>https://googleprojectzero.blogspot.com/2014/10/more-mac-os-x-and-iphone-sandbox.html</ref><ref>https://googleprojectzero.blogspot.com/2014/07/pwn4fun-spring-2014-safari-part-i_24.html</ref><ref>https://googleprojectzero.blogspot.com/2014/11/pwn4fun-spring-2014-safari-part-ii.html</ref> and features in comparison to their competition (like not being able to play WEBM files, sideloading being cockblocked on iOS, no calculator or weather app on tablets), and are thought of more so as status symbols for [[Nigger|niggers]] and [[India|street shitters]] who need to hide their poverty than actual useful tech products (like muh IBM ThinkPads). Hence, users of these products are often derided, rightfully so, especially since they are usually rather homosexual as well (they just are, okay). | [[Brimstone|Apple products]] are generally known to be overpriced<ref>https://www.youtube.com/watch?v=VMOBTyJbu1A</ref><ref>https://www.youtube.com/watch?v=eKm5-jUTRMM</ref>, fragile<ref>https://www.youtube.com/watch?v=AUaJ8pDlxi8</ref><ref>https://www.youtube.com/watch?v=GuWUUTNg9r4</ref><ref>https://www.youtube.com/watch?v=44DEgUXREUQ</ref><ref>https://www.youtube.com/watch?v=0qbrLiGY4Cg</ref><ref>https://www.youtube.com/watch?v=AH5F73qPtQQ</ref>, unrepairable<ref>https://www.youtube.com/watch?v=7cNg_ifibCQ</ref><ref>https://www.youtube.com/watch?v=qV4_mLw2BGM</ref><ref>https://www.youtube.com/watch?v=iiCBYAP_Sgg</ref><ref>https://www.youtube.com/watch?v=MUifN6abtSI</ref><ref>https://www.youtube.com/watch?v=RIFQC8iA65k</ref><ref>https://www.youtube.com/watch?v=RYG4VMqatEY</ref>, lacking in security<ref>https://www.kaspersky.com/blog/iphone-illusion-of-security/49145/</ref><ref>https://google.github.io/security-research/pocs/linux/bleedingtooth/writeup.html</ref><ref>https://www.youtube.com/watch?v=whhPipa6sBc</ref><ref>https://www.youtube.com/watch?v=FCSCq5rGxDI</ref><ref>https://googleprojectzero.blogspot.com/2023/10/an-analysis-of-an-in-the-wild-ios-safari-sandbox-escape.html</ref><ref>https://googleprojectzero.blogspot.com/2022/04/cve-2021-1782-ios-in-wild-vulnerability.html</ref><ref>https://googleprojectzero.blogspot.com/2021/12/a-deep-dive-into-nso-zero-click.html</ref><ref>https://googleprojectzero.blogspot.com/2020/12/an-ios-zero-click-radio-proximity.html</ref><ref>https://googleprojectzero.blogspot.com/2020/01/remote-iphone-exploitation-part-1.html</ref><ref>https://googleprojectzero.blogspot.com/2020/01/remote-iphone-exploitation-part-2.html</ref><ref>https://googleprojectzero.blogspot.com/2020/01/remote-iphone-exploitation-part-3.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/implant-teardown.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-1.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-2.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-3.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-4.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-5.html</ref><ref>https://googleprojectzero.blogspot.com/2019/08/a-very-deep-dive-into-ios-exploit.html</ref><ref>https://googleprojectzero.blogspot.com/2014/10/more-mac-os-x-and-iphone-sandbox.html</ref><ref>https://googleprojectzero.blogspot.com/2014/07/pwn4fun-spring-2014-safari-part-i_24.html</ref><ref>https://googleprojectzero.blogspot.com/2014/11/pwn4fun-spring-2014-safari-part-ii.html</ref> and features in comparison to their competition (like not being able to play WEBM files, sideloading being cockblocked on iOS, no calculator or weather app on tablets), and are thought of more so as status symbols for [[Nigger|niggers]] and [[India|street shitters]] who need to hide their poverty than actual useful tech products (like muh IBM ThinkPads). Hence, users of these products are often derided, rightfully so, especially since they are usually rather homosexual as well (they just are, okay). Using iDevices will gurantee you brainrot that forces you to assert dominance over anyone who prefers an actually usable product and deny all criticisms with Apple. | ||
== On the ‘cuck == | == On the ‘cuck == | ||
Revision as of 07:37, 15 February 2024

|
please click here and slowly scroll down to the bottom of the page. |

iToddler is a common insult levied towards users of Apple products on the ‘cuck and the ‘ty. /g/ users especially love using it, usually in response to fags like Jay Louis Irwin, or posts with iPhone filenames (e.g. "IMG_1488", or "B383-3722-3828-HE38-W2828").
Origins
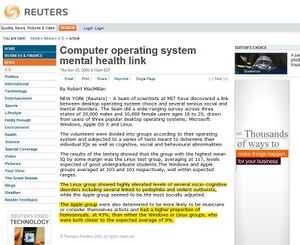
Apple products are generally known to be overpriced[1][2], fragile[3][4][5][6][7], unrepairable[8][9][10][11][12][13], lacking in security[14][15][16][17][18][19][20][21][22][23][24][25][26][27][28][29][30][31][32][33][34] and features in comparison to their competition (like not being able to play WEBM files, sideloading being cockblocked on iOS, no calculator or weather app on tablets), and are thought of more so as status symbols for niggers and street shitters who need to hide their poverty than actual useful tech products (like muh IBM ThinkPads). Hence, users of these products are often derided, rightfully so, especially since they are usually rather homosexual as well (they just are, okay). Using iDevices will gurantee you brainrot that forces you to assert dominance over anyone who prefers an actually usable product and deny all criticisms with Apple.
On the ‘cuck
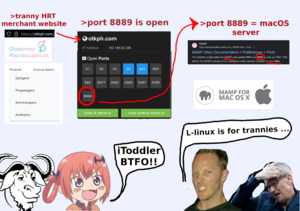
nu-/g/ is filled with iToddlers, all of which are known to be faggot pedophiles (they just are, okay). One of them is known to spend every day of the month creating shill threads and samefagging in /spg/ (smartphone general).
-
/spg/'s resident iToddler, caught red-handed while trying to samefag.
Citations
- ↑ https://www.youtube.com/watch?v=VMOBTyJbu1A
- ↑ https://www.youtube.com/watch?v=eKm5-jUTRMM
- ↑ https://www.youtube.com/watch?v=AUaJ8pDlxi8
- ↑ https://www.youtube.com/watch?v=GuWUUTNg9r4
- ↑ https://www.youtube.com/watch?v=44DEgUXREUQ
- ↑ https://www.youtube.com/watch?v=0qbrLiGY4Cg
- ↑ https://www.youtube.com/watch?v=AH5F73qPtQQ
- ↑ https://www.youtube.com/watch?v=7cNg_ifibCQ
- ↑ https://www.youtube.com/watch?v=qV4_mLw2BGM
- ↑ https://www.youtube.com/watch?v=iiCBYAP_Sgg
- ↑ https://www.youtube.com/watch?v=MUifN6abtSI
- ↑ https://www.youtube.com/watch?v=RIFQC8iA65k
- ↑ https://www.youtube.com/watch?v=RYG4VMqatEY
- ↑ https://www.kaspersky.com/blog/iphone-illusion-of-security/49145/
- ↑ https://google.github.io/security-research/pocs/linux/bleedingtooth/writeup.html
- ↑ https://www.youtube.com/watch?v=whhPipa6sBc
- ↑ https://www.youtube.com/watch?v=FCSCq5rGxDI
- ↑ https://googleprojectzero.blogspot.com/2023/10/an-analysis-of-an-in-the-wild-ios-safari-sandbox-escape.html
- ↑ https://googleprojectzero.blogspot.com/2022/04/cve-2021-1782-ios-in-wild-vulnerability.html
- ↑ https://googleprojectzero.blogspot.com/2021/12/a-deep-dive-into-nso-zero-click.html
- ↑ https://googleprojectzero.blogspot.com/2020/12/an-ios-zero-click-radio-proximity.html
- ↑ https://googleprojectzero.blogspot.com/2020/01/remote-iphone-exploitation-part-1.html
- ↑ https://googleprojectzero.blogspot.com/2020/01/remote-iphone-exploitation-part-2.html
- ↑ https://googleprojectzero.blogspot.com/2020/01/remote-iphone-exploitation-part-3.html
- ↑ https://googleprojectzero.blogspot.com/2019/08/implant-teardown.html
- ↑ https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-1.html
- ↑ https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-2.html
- ↑ https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-3.html
- ↑ https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-4.html
- ↑ https://googleprojectzero.blogspot.com/2019/08/in-wild-ios-exploit-chain-5.html
- ↑ https://googleprojectzero.blogspot.com/2019/08/a-very-deep-dive-into-ios-exploit.html
- ↑ https://googleprojectzero.blogspot.com/2014/10/more-mac-os-x-and-iphone-sandbox.html
- ↑ https://googleprojectzero.blogspot.com/2014/07/pwn4fun-spring-2014-safari-part-i_24.html
- ↑ https://googleprojectzero.blogspot.com/2014/11/pwn4fun-spring-2014-safari-part-ii.html